Answer to Question 1
TRUE
Answer to Question 2
The Internet of Things (IoT) involves the use of the Internet to connect a wide variety of sensors, devices, and machines, and is powering the development of a multitude of smart connected things, such as home electronics (smart TVs, thermostats, home security systems, and more), connected cars, medical devices and industrial equipment that supports manufacturing, energy, transportation, and other industrial sectors. IoT raises a host of security issues that are in some ways similar to existing security issues, but even more challenging, given the need to deal with a wider range of devices, operating in a less controlled, global environment, and with an expanded range of attack. In a world of connected things, the devices, the data produced and used by the devices, and the systems and applications supported by those devices, can all potentially be attacked. IoT poses several unique security challenges. For instance, many IoT devices, such as sensors, are intended to be deployed on a much greater scale than traditional Internet-connected devices, creating a vast quantity of interconnected links that can be exploited.
Existing tools, methods, and strategies need to be developed to deal with this unprecedented scale. Many instances of IoT consist of collections of identical devices that all have the same characteristics, which magnifies the potential impact of security vulnerabilities. Many IoT devices are anticipated to have a much longer service life than typical equipment, which raises the possibility that devices may outlive manufacturer, leaving them without long-term support that creates persistent vulnerabilities. Many IoT devices are intentionally designed without the ability to be upgraded, or the upgrade process is difficult, which raises the possibility that vulnerable devices cannot or will not be fixed, leaving them perpetually vulnerable. Many IoT devices do not provide the user with visibility into the workings of the device or the data being produced, nor alert the user when a security problem arises, so users may believe an IoT device is functioning as intended when in fact, it may be performing in a malicious manner. Finally, some IoT devices, such as sensors, are unobtrusively embedded in the environment such that a user may not even be aware of the device, so a security breach might persist for a long time before being noticed.
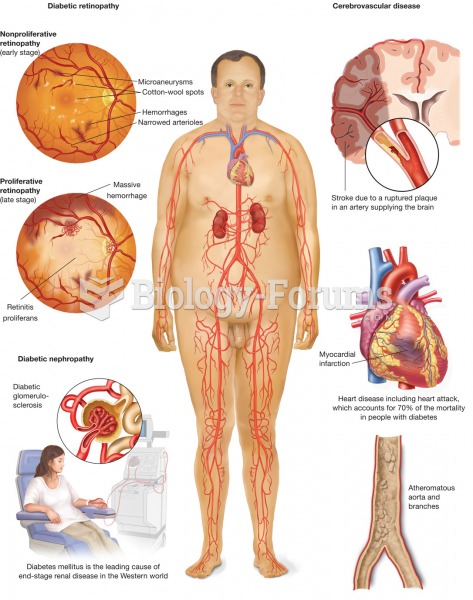 Diabetes mellitus. The metabolic disease diabetes mellitus, with symptoms of polydipsia, polyuria, a
Diabetes mellitus. The metabolic disease diabetes mellitus, with symptoms of polydipsia, polyuria, a
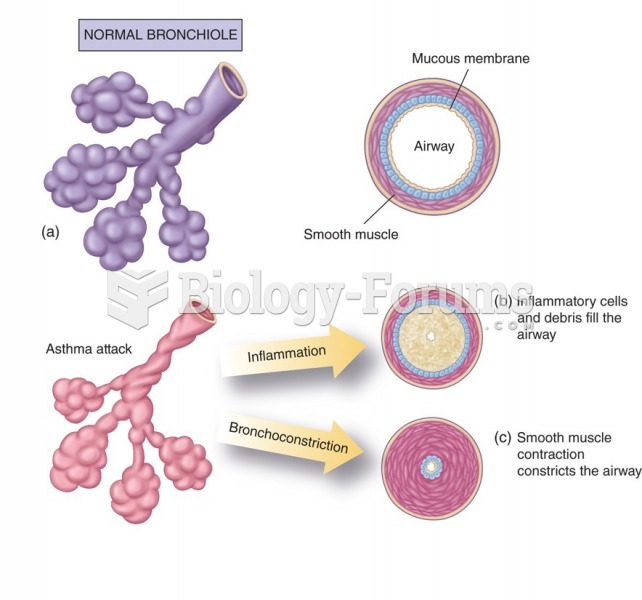
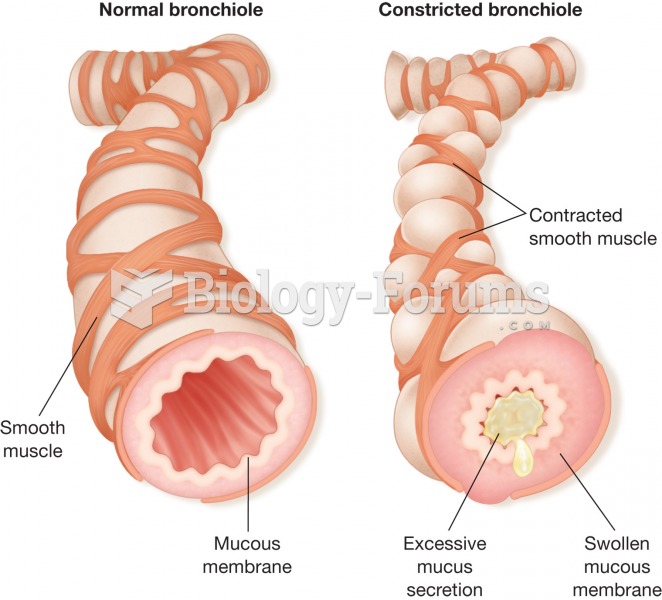 Asthma. (a) A normal bronchiole. (b) An asthmatic bronchiole. During an asthma “attack,” the bronchi
Asthma. (a) A normal bronchiole. (b) An asthmatic bronchiole. During an asthma “attack,” the bronchi