|
|
|
Signs and symptoms of a drug overdose include losing consciousness, fever or sweating, breathing problems, abnormal pulse, and changes in skin color.
More than 34,000 trademarked medication names and more than 10,000 generic medication names are in use in the United States.
Drug-induced pharmacodynamic effects manifested in older adults include drug-induced renal toxicity, which can be a major factor when these adults are experiencing other kidney problems.
The cure for trichomoniasis is easy as long as the patient does not drink alcoholic beverages for 24 hours. Just a single dose of medication is needed to rid the body of the disease. However, without proper precautions, an individual may contract the disease repeatedly. In fact, most people develop trichomoniasis again within three months of their last treatment.
Most childhood vaccines are 90–99% effective in preventing disease. Side effects are rarely serious.
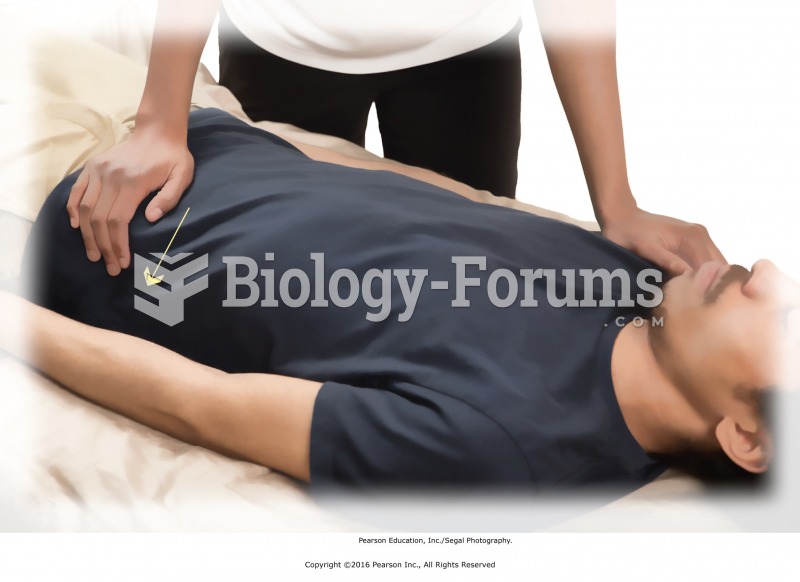
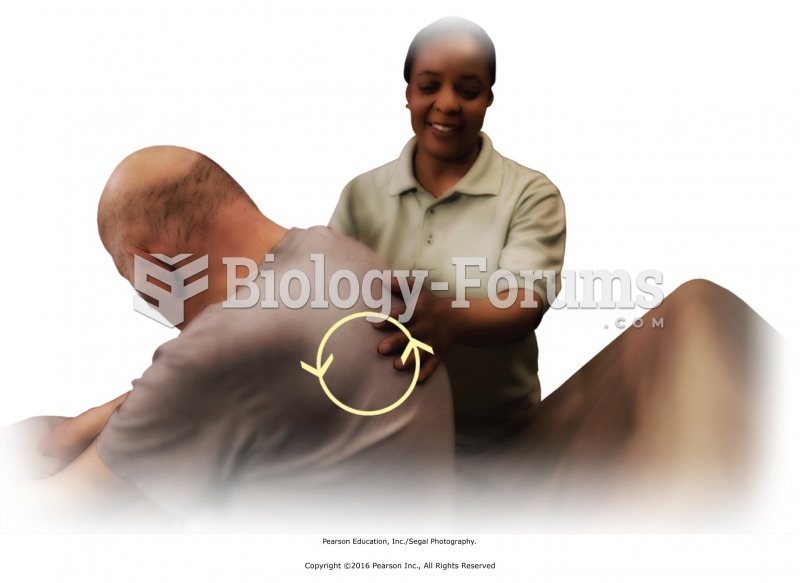 Apply superficial friction to the upper and lower back. Stand to one side. Ask the recipient to lean ...
Apply superficial friction to the upper and lower back. Stand to one side. Ask the recipient to lean ...
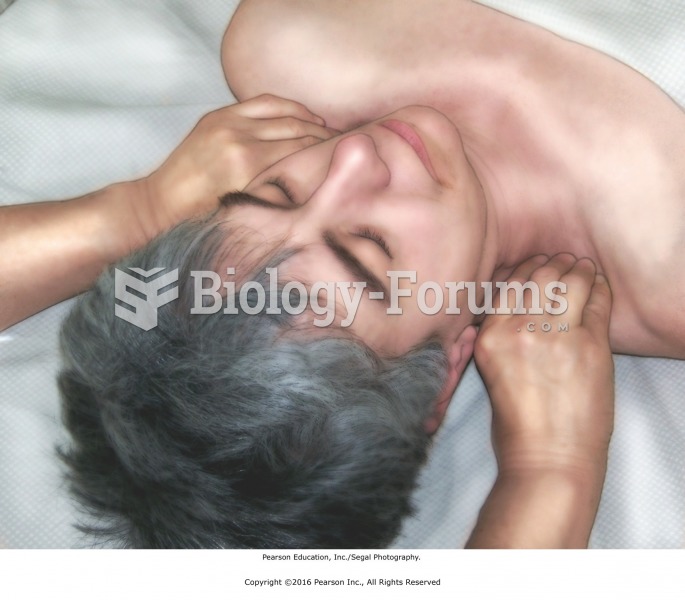 Ayurvedic massage. Pressing the ansa marma on the front and back of the shoulders with recipient ...
Ayurvedic massage. Pressing the ansa marma on the front and back of the shoulders with recipient ...