|
|
|
One way to reduce acid reflux is to lose two or three pounds. Most people lose weight in the belly area first when they increase exercise, meaning that heartburn can be reduced quickly by this method.
The eye muscles are the most active muscles in the whole body. The external muscles that move the eyes are the strongest muscles in the human body for the job they have to do. They are 100 times more powerful than they need to be.
Nearly 31 million adults in America have a total cholesterol level that is more than 240 mg per dL.
Adults are resistant to the bacterium that causes Botulism. These bacteria thrive in honey – therefore, honey should never be given to infants since their immune systems are not yet resistant.
Less than one of every three adults with high LDL cholesterol has the condition under control. Only 48.1% with the condition are being treated for it.
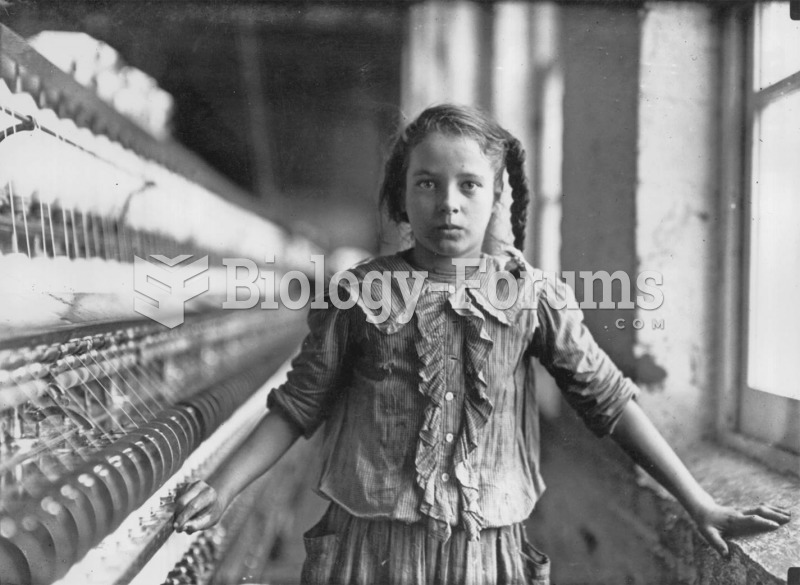 This girl ran four spinning machines in a cotton mill in Whitnel, North Carolina. Only 4 feet, 3 inc
This girl ran four spinning machines in a cotton mill in Whitnel, North Carolina. Only 4 feet, 3 inc
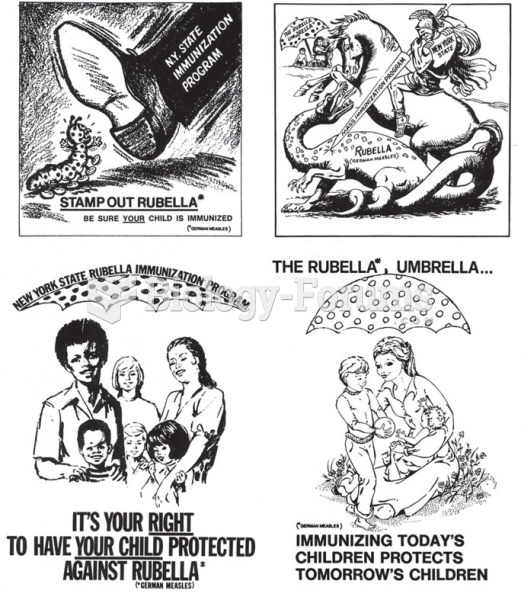 Ads from the public service campaign in the late 1960s and early 1970s that encouraged people to get ...
Ads from the public service campaign in the late 1960s and early 1970s that encouraged people to get ...