|
|
|
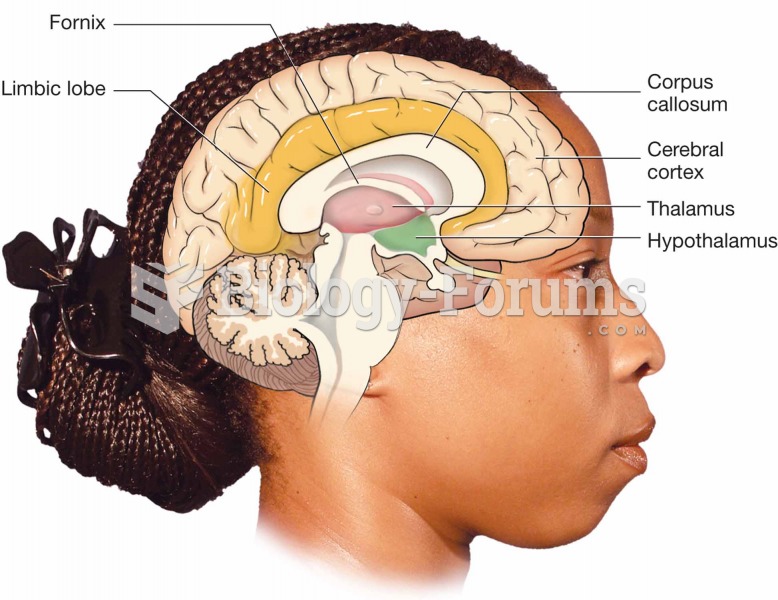
Human neurons are so small that they require a microscope in order to be seen. However, some neurons can be up to 3 feet long, such as those that extend from the spinal cord to the toes.
Adolescents often feel clumsy during puberty because during this time of development, their hands and feet grow faster than their arms and legs do. The body is therefore out of proportion. One out of five adolescents actually experiences growing pains during this period.
Critical care patients are twice as likely to receive the wrong medication. Of these errors, 20% are life-threatening, and 42% require additional life-sustaining treatments.
According to the American College of Allergy, Asthma & Immunology, more than 50 million Americans have some kind of food allergy. Food allergies affect between 4 and 6% of children, and 4% of adults, according to the CDC. The most common food allergies include shellfish, peanuts, walnuts, fish, eggs, milk, and soy.
In Eastern Europe and Russia, interferon is administered intranasally in varied doses for the common cold and influenza. It is claimed that this treatment can lower the risk of infection by as much as 60–70%.