|
|
|
Amoebae are the simplest type of protozoans, and are characterized by a feeding and dividing trophozoite stage that moves by temporary extensions called pseudopodia or false feet.
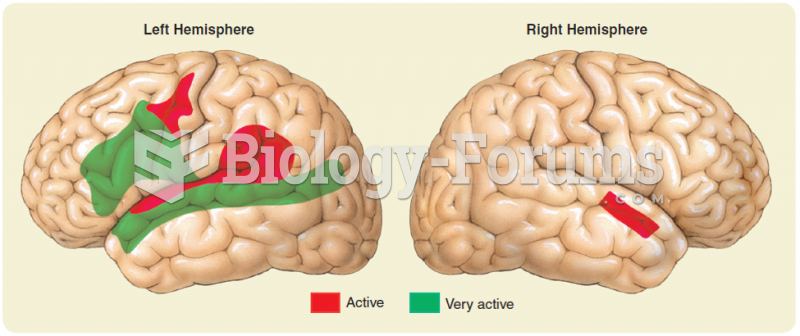
There are immediate benefits of chiropractic adjustments that are visible via magnetic resonance imaging (MRI). It shows that spinal manipulation therapy is effective in decreasing pain and increasing the gaps between the vertebrae, reducing pressure that leads to pain.
The ratio of hydrogen atoms to oxygen in water (H2O) is 2:1.
Stevens-Johnson syndrome and Toxic Epidermal Necrolysis syndrome are life-threatening reactions that can result in death. Complications include permanent blindness, dry-eye syndrome, lung damage, photophobia, asthma, chronic obstructive pulmonary disease, permanent loss of nail beds, scarring of mucous membranes, arthritis, and chronic fatigue syndrome. Many patients' pores scar shut, causing them to retain heat.
In the United States, an estimated 50 million unnecessary antibiotics are prescribed for viral respiratory infections.
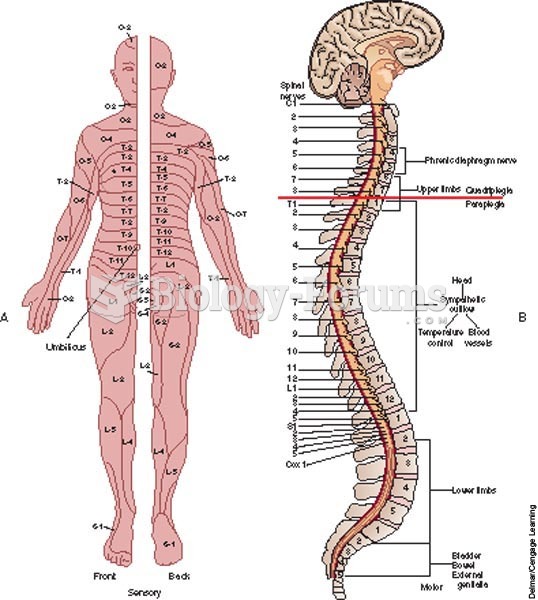 Spinal cord—levels of injury; A, areas of sensory function (dermatomes); B, areas of motor function.
Spinal cord—levels of injury; A, areas of sensory function (dermatomes); B, areas of motor function.
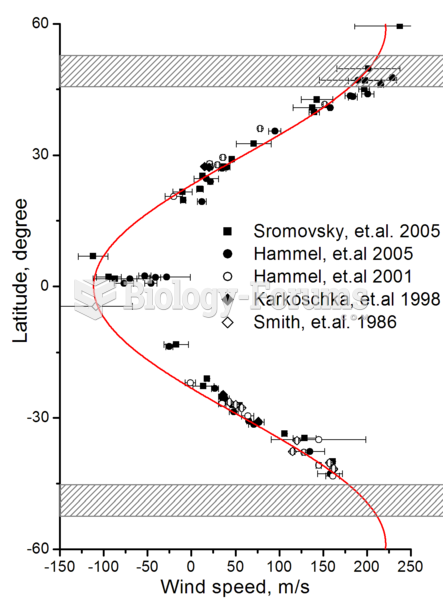 Zonal wind speeds on Uranus. Shaded areas show the southern collar and its future northern counterpa
Zonal wind speeds on Uranus. Shaded areas show the southern collar and its future northern counterpa