|
|
|
Historic treatments for rheumatoid arthritis have included gold salts, acupuncture, a diet consisting of apples or rhubarb, nutmeg, nettles, bee venom, bracelets made of copper, prayer, rest, tooth extractions, fasting, honey, vitamins, insulin, snow collected on Christmas, magnets, and electric convulsion therapy.
According to animal studies, the typical American diet is damaging to the liver and may result in allergies, low energy, digestive problems, and a lack of ability to detoxify harmful substances.
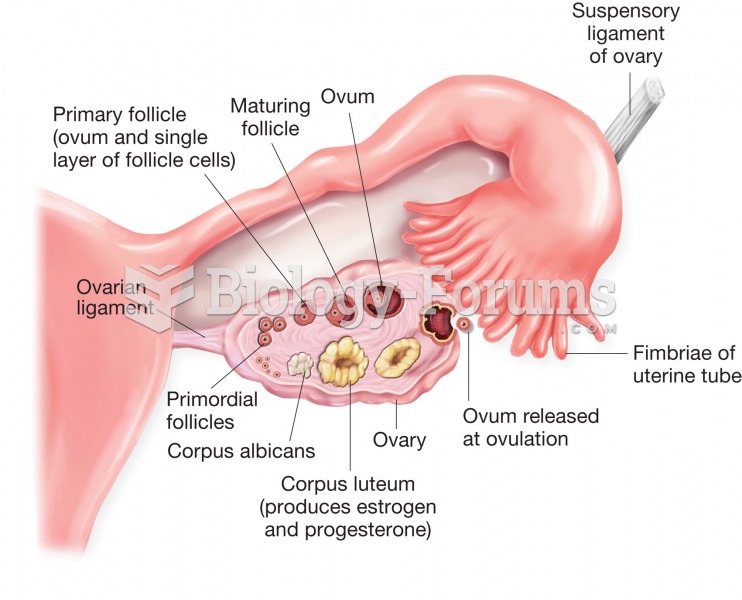
Approximately 15–25% of recognized pregnancies end in miscarriage. However, many miscarriages often occur before a woman even knows she is pregnant.
Thyroid conditions may make getting pregnant impossible.
It is believed that humans initially contracted crabs from gorillas about 3 million years ago from either sleeping in gorilla nests or eating the apes.