|
|
|
Asthma cases in Americans are about 75% higher today than they were in 1980.
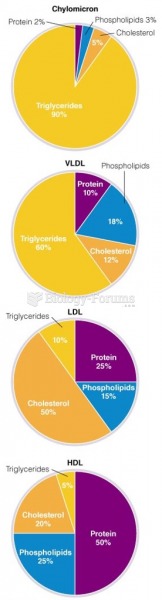
It is important to read food labels and choose foods with low cholesterol and saturated trans fat. You should limit saturated fat to no higher than 6% of daily calories.
The most dangerous mercury compound, dimethyl mercury, is so toxic that even a few microliters spilled on the skin can cause death. Mercury has been shown to accumulate in higher amounts in the following types of fish than other types: swordfish, shark, mackerel, tilefish, crab, and tuna.
Asthma-like symptoms were first recorded about 3,500 years ago in Egypt. The first manuscript specifically written about asthma was in the year 1190, describing a condition characterized by sudden breathlessness. The treatments listed in this manuscript include chicken soup, herbs, and sexual abstinence.
People who have myopia, or nearsightedness, are not able to see objects at a distance but only up close. It occurs when the cornea is either curved too steeply, the eye is too long, or both. This condition is progressive and worsens with time. More than 100 million people in the United States are nearsighted, but only 20% of those are born with the condition. Diet, eye exercise, drug therapy, and corrective lenses can all help manage nearsightedness.