This topic contains a solution. Click here to go to the answer
|
|
|
Did you know?
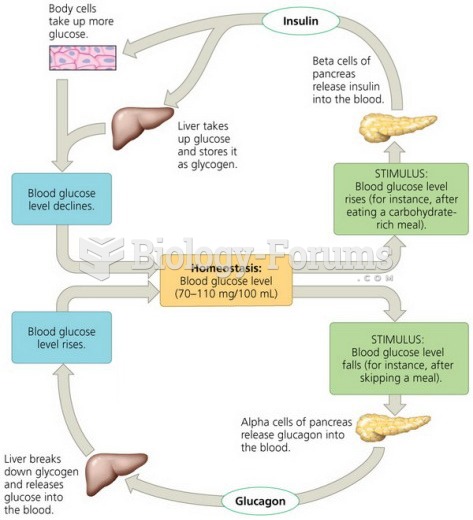
More than one-third of adult Americans are obese. Diseases that kill the largest number of people annually, such as heart disease, cancer, diabetes, stroke, and hypertension, can be attributed to diet.
Did you know?
More than 4.4billion prescriptions were dispensed within the United States in 2016.
Did you know?
Earwax has antimicrobial properties that reduce the viability of bacteria and fungus in the human ear.
Did you know?
Throughout history, plants containing cardiac steroids have been used as heart drugs and as poisons (e.g., in arrows used in combat), emetics, and diuretics.
Did you know?
The top five reasons that children stay home from school are as follows: colds, stomach flu (gastroenteritis), ear infection (otitis media), pink eye (conjunctivitis), and sore throat.