|
|
|
There are more bacteria in your mouth than there are people in the world.
Drug abusers experience the following scenario: The pleasure given by their drug (or drugs) of choice is so strong that it is difficult to eradicate even after years of staying away from the substances involved. Certain triggers may cause a drug abuser to relapse. Research shows that long-term drug abuse results in significant changes in brain function that persist long after an individual stops using drugs. It is most important to realize that the same is true of not just illegal substances but alcohol and tobacco as well.
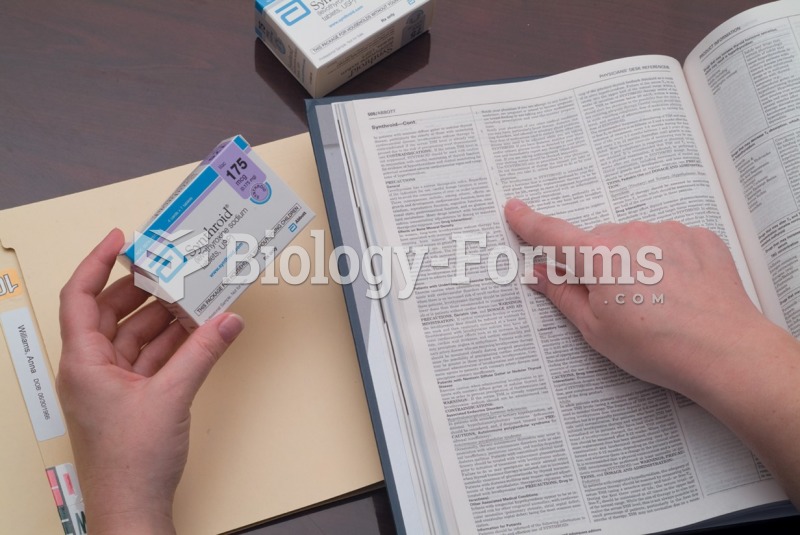
The term pharmacology is derived from the Greek words pharmakon("claim, medicine, poison, or remedy") and logos ("study").
Studies show that systolic blood pressure can be significantly lowered by taking statins. In fact, the higher the patient's baseline blood pressure, the greater the effect of statins on his or her blood pressure.
Medication errors are more common among seriously ill patients than with those with minor conditions.