|
|
|
There are approximately 3 million unintended pregnancies in the United States each year.
Parkinson's disease is both chronic and progressive. This means that it persists over a long period of time and that its symptoms grow worse over time.
The senior population grows every year. Seniors older than 65 years of age now comprise more than 13% of the total population. However, women outlive men. In the 85-and-over age group, there are only 45 men to every 100 women.
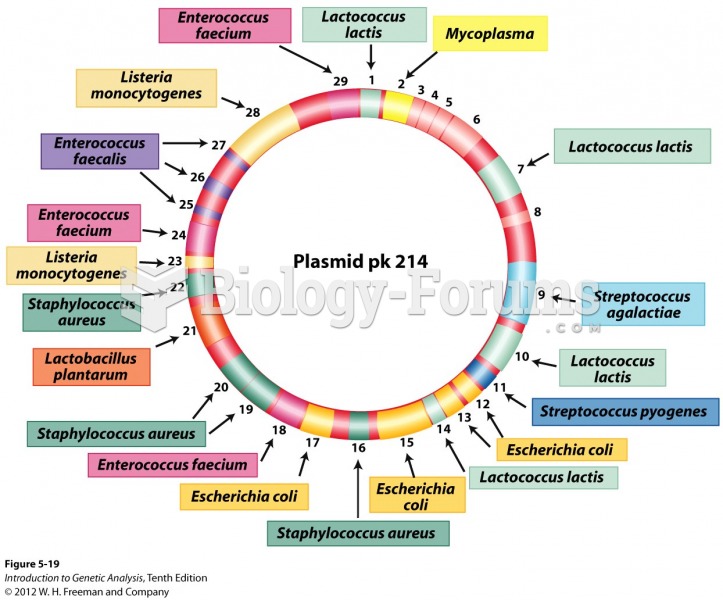
People often find it difficult to accept the idea that bacteria can be beneficial and improve health. Lactic acid bacteria are good, and when eaten, these bacteria improve health and increase longevity. These bacteria included in foods such as yogurt.
Bisphosphonates were first developed in the nineteenth century. They were first investigated for use in disorders of bone metabolism in the 1960s. They are now used clinically for the treatment of osteoporosis, Paget's disease, bone metastasis, multiple myeloma, and other conditions that feature bone fragility.