|
|
|
Individuals are never “cured” of addictions. Instead, they learn how to manage their disease to lead healthy, balanced lives.
Every 10 seconds, a person in the United States goes to the emergency room complaining of head pain. About 1.2 million visits are for acute migraine attacks.
About one in five American adults and teenagers have had a genital herpes infection—and most of them don't know it. People with genital herpes have at least twice the risk of becoming infected with HIV if exposed to it than those people who do not have genital herpes.
In most cases, kidneys can recover from almost complete loss of function, such as in acute kidney (renal) failure.
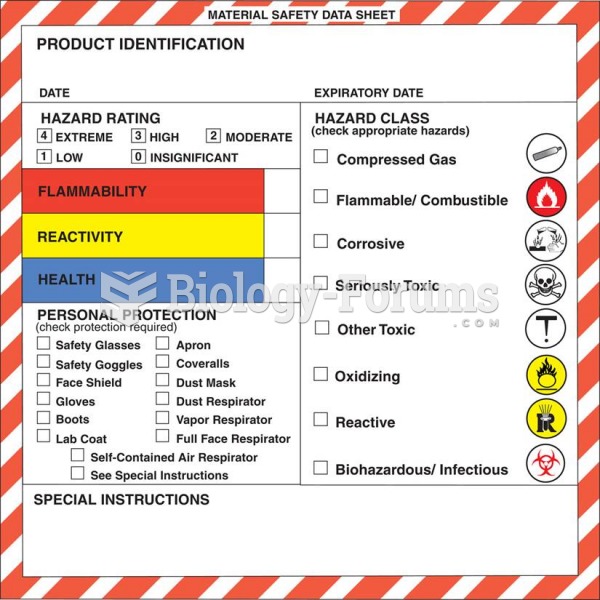
Ether was used widely for surgeries but became less popular because of its flammability and its tendency to cause vomiting. In England, it was quickly replaced by chloroform, but this agent caused many deaths and lost popularity.