|
|
|
Drug abusers experience the following scenario: The pleasure given by their drug (or drugs) of choice is so strong that it is difficult to eradicate even after years of staying away from the substances involved. Certain triggers may cause a drug abuser to relapse. Research shows that long-term drug abuse results in significant changes in brain function that persist long after an individual stops using drugs. It is most important to realize that the same is true of not just illegal substances but alcohol and tobacco as well.
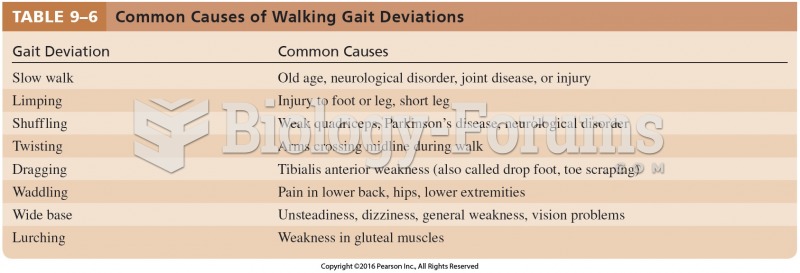
Elderly adults are at greatest risk of stroke and myocardial infarction and have the most to gain from prophylaxis. Patients ages 60 to 80 years with blood pressures above 160/90 mm Hg should benefit from antihypertensive treatment.
In women, pharmacodynamic differences include increased sensitivity to (and increased effectiveness of) beta-blockers, opioids, selective serotonin reuptake inhibitors, and typical antipsychotics.
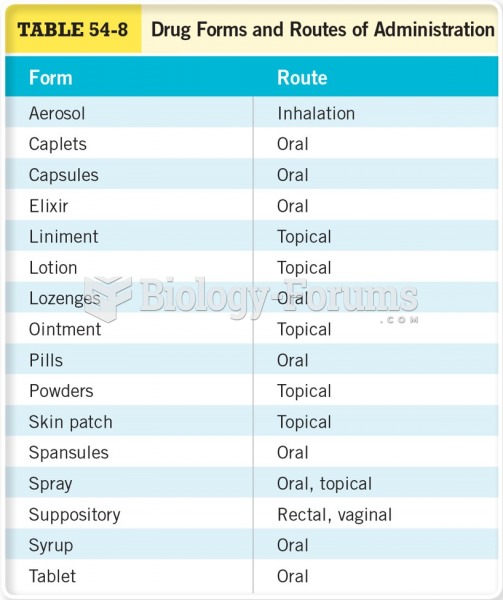
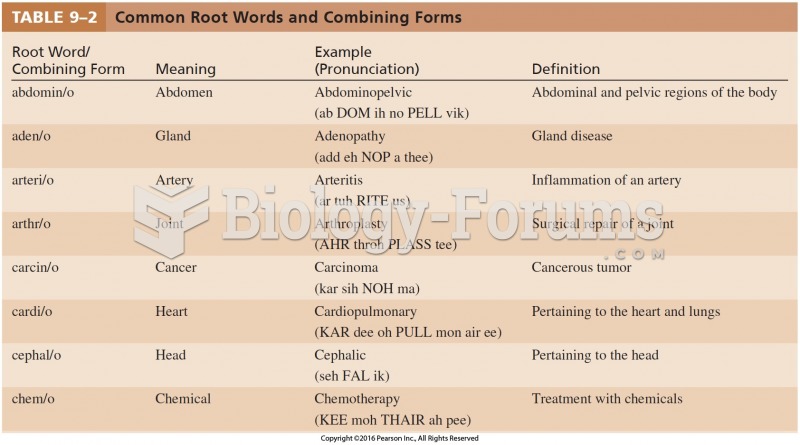
The term pharmacology is derived from the Greek words pharmakon("claim, medicine, poison, or remedy") and logos ("study").
A seasonal flu vaccine is the best way to reduce the chances you will get seasonal influenza and spread it to others.