|
|
|
Warfarin was developed as a consequence of the study of a strange bleeding disorder that suddenly occurred in cattle on the northern prairies of the United States in the early 1900s.
Normal urine is sterile. It contains fluids, salts, and waste products. It is free of bacteria, viruses, and fungi.
In the United States, there is a birth every 8 seconds, according to the U.S. Census Bureau's Population Clock.
According to the American College of Allergy, Asthma & Immunology, more than 50 million Americans have some kind of food allergy. Food allergies affect between 4 and 6% of children, and 4% of adults, according to the CDC. The most common food allergies include shellfish, peanuts, walnuts, fish, eggs, milk, and soy.
Patients who cannot swallow may receive nutrition via a parenteral route—usually, a catheter is inserted through the chest into a large vein going into the heart.
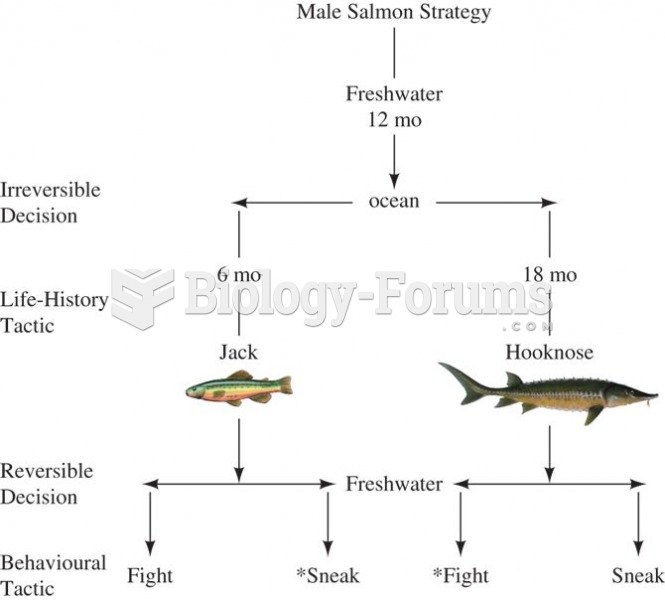 Male coho salmon exhibit two alternative life history strategies. “Jackâ€ÂÂ
Male coho salmon exhibit two alternative life history strategies. “Jackâ€ÂÂ
 This young boy with muscular dystrophy needs to receive tube feedings and home nursing care. He atte
This young boy with muscular dystrophy needs to receive tube feedings and home nursing care. He atte