|
|
|
All adverse reactions are commonly charted in red ink in the patient's record and usually are noted on the front of the chart. Failure to follow correct documentation procedures may result in malpractice lawsuits.
The National Institutes of Health have supported research into acupuncture. This has shown that acupuncture significantly reduced pain associated with osteoarthritis of the knee, when used as a complement to conventional therapies.
There are more sensory neurons in the tongue than in any other part of the body.
The training of an anesthesiologist typically requires four years of college, 4 years of medical school, 1 year of internship, and 3 years of residency.
Certain topical medications such as clotrimazole and betamethasone are not approved for use in children younger than 12 years of age. They must be used very cautiously, as directed by a doctor, to treat any child. Children have a much greater response to topical steroid medications.
 Charles Darwin may be dead and gone but a recent write-in campaign has pitted him against Republican
Charles Darwin may be dead and gone but a recent write-in campaign has pitted him against Republican
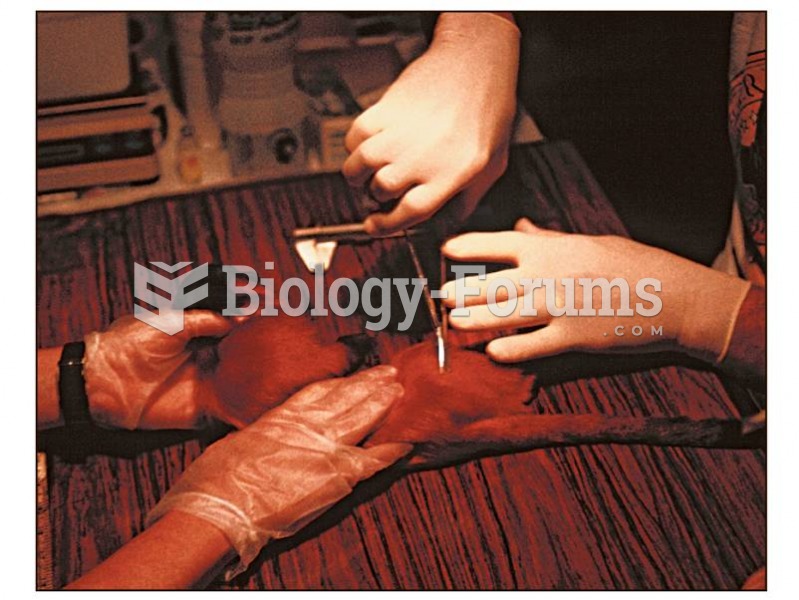 Modern primate study sometimes involves high-tech methods. This golden lion tamarin is having a batt
Modern primate study sometimes involves high-tech methods. This golden lion tamarin is having a batt