|
|
|
Dogs have been used in studies to detect various cancers in human subjects. They have been trained to sniff breath samples from humans that were collected by having them breathe into special tubes. These people included 55 lung cancer patients, 31 breast cancer patients, and 83 cancer-free patients. The dogs detected 54 of the 55 lung cancer patients as having cancer, detected 28 of the 31 breast cancer patients, and gave only three false-positive results (detecting cancer in people who didn't have it).
According to animal studies, the typical American diet is damaging to the liver and may result in allergies, low energy, digestive problems, and a lack of ability to detoxify harmful substances.
If you could remove all of your skin, it would weigh up to 5 pounds.
Acute bronchitis is an inflammation of the breathing tubes (bronchi), which causes increased mucus production and other changes. It is usually caused by bacteria or viruses, can be serious in people who have pulmonary or cardiac diseases, and can lead to pneumonia.
Most women experience menopause in their 50s. However, in 1994, an Italian woman gave birth to a baby boy when she was 61 years old.
 The Koala does not normally need to drink, because it can obtain all of the moisture it needs by eat
The Koala does not normally need to drink, because it can obtain all of the moisture it needs by eat
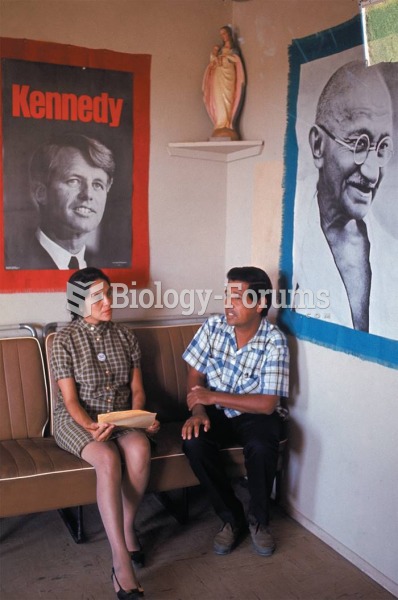 Dolores Huerta and Cesar Chavez, leaders of the United Farm Workers, discuss their 1968 strike of ...
Dolores Huerta and Cesar Chavez, leaders of the United Farm Workers, discuss their 1968 strike of ...