This topic contains a solution. Click here to go to the answer
|
|
|
Did you know?
The term pharmacology is derived from the Greek words pharmakon("claim, medicine, poison, or remedy") and logos ("study").
Did you know?
Human stomach acid is strong enough to dissolve small pieces of metal such as razor blades or staples.
Did you know?
In 2010, opiate painkllers, such as morphine, OxyContin®, and Vicodin®, were tied to almost 60% of drug overdose deaths.
Did you know?
Sperm cells are so tiny that 400 to 500 million (400,000,000–500,000,000) of them fit onto 1 tsp.
Did you know?
Many medications that are used to treat infertility are injected subcutaneously. This is easy to do using the anterior abdomen as the site of injection but avoiding the area directly around the belly button.
 Examining the survivorship curve of a Dall mountain sheep population reveals information on the caus
Examining the survivorship curve of a Dall mountain sheep population reveals information on the caus
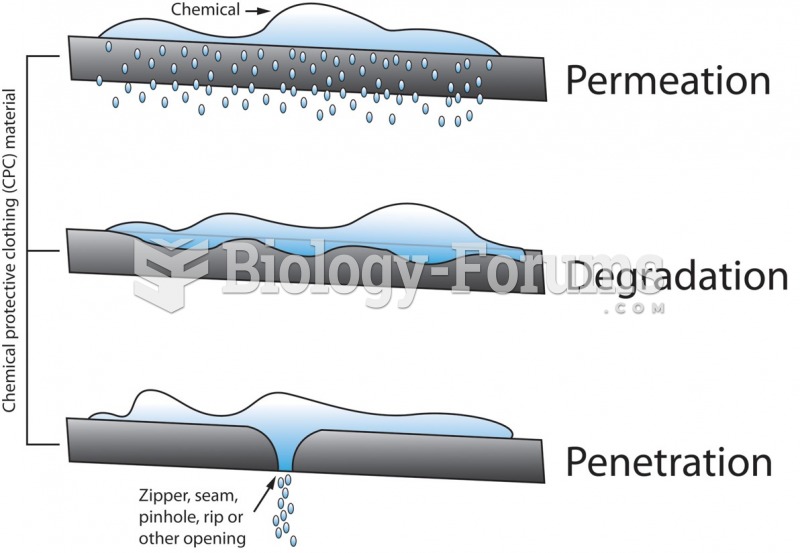
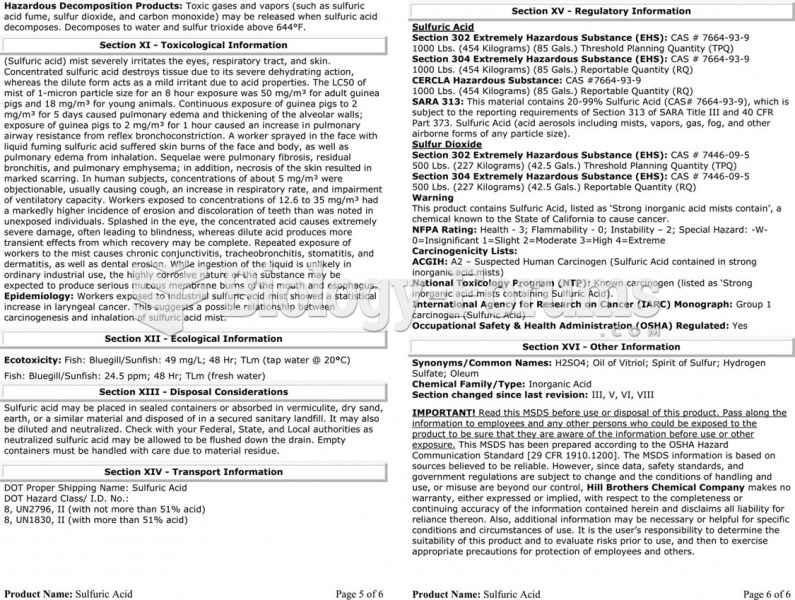 The material safety data sheet (MSDS) for sulfuric acid showing the detailed technical information ...
The material safety data sheet (MSDS) for sulfuric acid showing the detailed technical information ...